The way businesses use technology has completely changed over the last ten or fifteen years. Organizations have transitioned from localized physical machines to running entire operations on a distributed digital network. Yet, a lot of business owners are still stuck with an IT framework left over from 2010.
415 IT Blog
Most business owners assume that tighter security requires a slower user experience. They accept friction as the price of safety.
This mindset creates a dangerous paradox: when security is too difficult to use, your team becomes less secure. If logging in requires three different devices and ten minutes, employees will work around you. To eliminate this invisible productivity and security leak, you must remove friction.
How much of every week do you, or any of your employees, spend seeking out the information needed to get the job done… or trying to, at least, in between all the diversions and distractions. How often have you trawled through your digital storage, only to lose track of your progress when yet another chat notification drags your attention away from… what were you working on again?
How frustrating is it when your computer just doesn’t want to cooperate, whether it takes its sweet time starting up in the morning or decides to go on break in the middle of a meeting? How frustrating it is to see it happening to your team members, fully aware that they are feeling the same frustration you would? How much does it cost you, all events converging over time?
How much of a relief would it be if all these problems stemmed from one source: it being the time to retire that particular piece of hardware and replace it with something new?
For many, the introduction of remote or hybrid work practices was less of a choice and more of an existential need. Now, years after certain events caused this existential need, there are still pockets of friction that appear and make these approaches to work far more challenging than they can and should be.
Let’s explore a few of these pockets of friction and even more crucially, how to smooth them over.
How many passwords does anyone—you, your team, your family, your competitors—have to keep track of nowadays? According to research by password-management software NordPass, that number has actually decreased for the first time in years… their figures of 170 on average, 87 of which were business-related in 2024, shrank to 120 on average, 67 of which were work-related, earlier this year.
Granted, these figures were collected between April 4th and the 15th and included only 1509 users, so the statistical significance is questionable. Despite that, we can’t disagree with NordPass’ conclusion: more people are using password alternatives.
Business owners often make technology investments in a vacuum. You look at the metrics, you see the potential return on investment, and you purchase the platform. Two months later, everyone is still quietly reverting back to their old spreadsheets. You might want to mandate the new software and lock down the old files, but mandating the platform is not the core issue. The problem is that your team does not see the tool as a way to make their workdays easier.
How much does a 5-second lag on your technology cost? Most business owners will look at an aging laptop and think, “It still works, so why replace it?” The reality is that older devices can lead to a silent, invisible drain on your budget that doesn’t show up on the hardware invoice: the labor leak.
How often do you find yourself sitting in your car, coffee in the cupholder, dreading going into your own business just because you know that there will be some number of IT challenges and issues that you will have to deal with?
This is completely understandable… unless you happen to be working with a managed service provider.
Traditional antivirus relies on a database of known threat signatures to identify malicious files. While this method was effective a decade ago, it is now dangerously reactive. Modern cybercrime utilizes automated tools to generate malware that alters its digital signature every few seconds. This means a threat can bypass security measures before a definition update is ever released to your network.
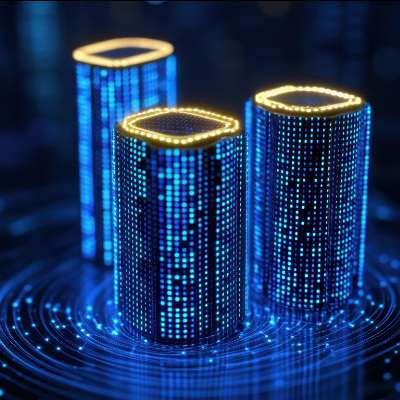
We’ve all seen the headlines about what AI can do; it can write your emails, analyze your spreadsheets, and even generate art in seconds. But we rarely talk about what it takes to make that happen. When you ask a chatbot a question, you aren't just tapping into a "brain" in the cloud; you are triggering a massive, physical chain reaction of resource consumption.
Ask a handful of IT consultants to explain the cloud, and you’ll likely be met with a blizzard of buzzwords—”scalability,”“elasticity,” and “hybrid infrastructure”—that do very little to help you hit your quarterly goals.
All the noise aside, the cloud isn’t a mystery; it’s simply renting someone else's computer. Instead of maintaining a server box in your broom closet, you are leasing space on high-performance machines owned by giants like Microsoft, Amazon, or Google. They own the hardware; you own the results.
Nowadays, it’s common for business tools to incorporate AI into their already helpful features. Google Docs is a prime example. As of the time of this writing, Google has recently added a “Help me create” function that can help you get a start on your next project.
Let’s take a look at how it works and how you could potentially utilize it to your advantage.
When you think of business technology, what’s the impression you get? Do you look at it as a pain in the neck obligation, an unavoidable cost, or one of your most valuable assets?
For many, it is the former… but for the most successful among us, it is the latter. Let’s talk about how you can use your technology to optimize your incoming cash flow.
Most business owners I talk to have some form of backup. Maybe it's an external drive plugged into a server, or perhaps everything is saved in the cloud. While these are great starts, they often have a single point of failure. If your office has a fire, that external drive is gone. If a user accidentally deletes a folder and it syncs to the cloud, that data might be gone before you notice.
To make a backup "trustworthy," we use a framework called the 3-2-1-1 Rule. It sounds like a football play, but it’s actually a recipe for peace of mind.
It’s almost impossible to find a workplace these days where mobile devices aren’t part of the furniture. We use them for everything from checking email between meetings to approving contracts while waiting for a latte. When done right, giving your team the ability to work from anywhere is a massive win for productivity.
Cybersecurity can often feel like a complex web of buzzwords, but professionals actually rely on a simple framework called the CIA Triad to stay safe. This doesn't refer to the intelligence agency; instead, it stands for Confidentiality, Integrity, and Availability. You can think of these three pillars as the locks, the reinforced walls, and the key to the vault. If any one of these pillars fails, the entire system is at risk.