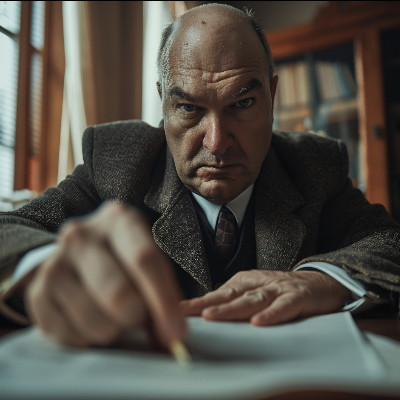
How often do you find yourself sitting in your car, coffee in the cupholder, dreading going into your own business just because you know that there will be some number of IT challenges and issues that you will have to deal with?
This is completely understandable… unless you happen to be working with a managed service provider.