Staying proactive with your IT maintenance can save your business a lot of money, but a lot of people don’t know exactly how they can go about doing this. In this month’s newsletter we are going to discuss how proactive maintenance works and how it is a crucial part to any evolved managed IT strategy.
415 IT Blog
Many businesses struggle with IT maintenance and management. Maybe they don’t have the resources to perform in-house maintenance due to a lack of funding and, consequently, the inability to hire full-time technicians. Maybe they believe that their technology is perfectly fine as is and doesn’t require regular maintenance. We’re here to burst that bubble; you should always have maintenance at the top of mind, and in today’s business environment, there is no excuse not to.
It’s imperative that you keep your IT infrastructure under control, but many organizations push it to the side. The problem is that ignoring IT often makes it so that you aren’t properly evaluating your technology infrastructure and support, meaning that you could be wasting time and resources that would be better spent elsewhere. Ask yourself the following questions to determine whether or not your IT systems are being maintained properly.
There are certain processes within an organization that take a considerable amount of time to do. These include applying patches, monitoring network traffic, and updating software as needed. While it might seem like something your business can handle on its own, some small organizations struggle to accomplish everything they set out to do--especially with a limited budget or workforce. Our staff’s powerful monitoring and management tool can aid in this initiative.
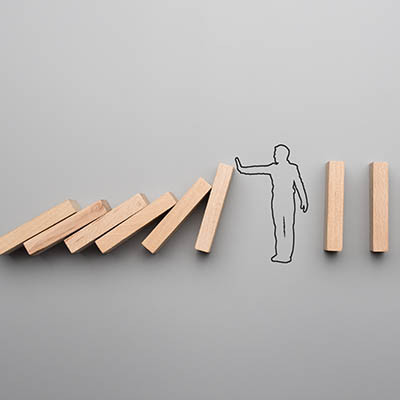
If your business experiences a technological failure, how many operations simply stop dead in their tracks until the problem is resolved? While it might seem like you have no control over your business’ technology (at least the issues that cause downtime), this is far from the truth. If you take action now, you can prevent issues from cropping up in the first place rather than reacting to them later, after they have already caused considerable problems for your business.
Network security is an important part of keeping both your business and your staff away from online threats, but it’s not enough to implement the best, most comprehensive solutions on the market. There are a surprising number of facets to network security, and in order to optimize protection against online threats, you’ll need to know all of them. Thankfully, you don’t have to do this alone.
Today’s businesses still require a lot of hardwork and dedication, but technology assists with day-to-day tasks, and gives more opportunities than we could otherwise imagine. As such, it needs to be in optimal shape, but what business has the time to see to that? Well, with the help of remote monitoring and management, yours does.
“The good old days” usually refer to times long past, where things were more simple. Businesses a few decades ago didn’t have much complex technology in their office, but nowadays organizations have multiple server units and plenty of workstations--all of which need more maintenance than ever before. What’s the best way for your organization to approach IT maintenance?